Anatomy of a phishing email
Using the clues hiding in plain sight, I’ll show you how to see that’s NOT a real Outlook Office 365 warning.
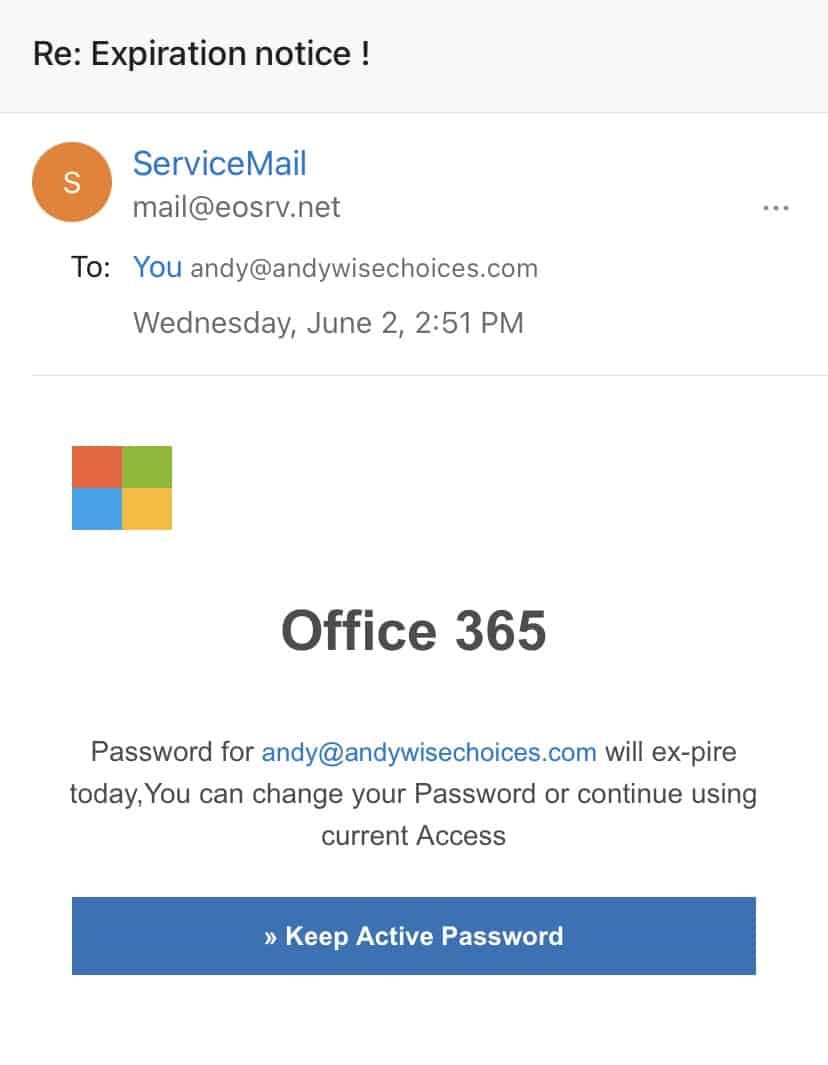
The screenshot you see on this post came from an unsolicited email I received in my Outlook inbox. It had a tone of dread — my Office 365 password is about to expire, oh my! — and it prompted me to click on the blue box to “keep (my) active password.”
First of all, no email service will ever “expire” your password. It’s YOURS. An email service may recommend or suggest a stronger password, but it will never “expire” the password you came up with — not to mention offer you a method to keep your password after threatening its expiration. So is it expiring or not?!
The answer is it’s NOT. Here’s how you can tell by the very things that appear in that email:
- MISSPELLINGS & GRAMMATICAL ERRORS. Look at how the email spells expire as “ex-pire.” Or how it unnecessarily capitalizes the words “Password” and “Access.” Even in the subject line, the exclamation point (!) is spaced too many times from the words “Expiration notice.” Each is a sign of a lazy scammer’s sentence structure.
- MISMATCHED SENDER’S EMAIL ADDRESS. When I clicked on that “ServiceMail” sender’s ID to reveal the sender’s email address, it displayed “mail@eosrv.net.” If it really was from Outlook, which is a Microsoft product, it would have been from an address that ends in either microsoft.com or justanswer.com, Microsoft’s dedicated Outlook app support platform.
Sources at DigitalCheck.com suggested I find out where that “Keep Active Password” link leads.
‘Wait a minute. Andy always warns me to never click on a link from an unsolicited email I believe to be a phishing scam!’
That’s true. That warning still stands. So how do you figure out where that link leads without clicking on it and risking the launch of spyware or malware on your computer?
“The simplest way is to hover your mouse over the link (or button) without clicking it,” wrote DigitalCheck.com in this blog about how to spot phishing scams. When you do that, the real destination of the link pops up, usually a gobbledegook URL that looks like code.
So how do you make sense of what pops up?
“Ignore anything that comes before the second-to-last dot in the URL. Also ignore whatever comes after the first (single) slash in the address,” DigitalCheck.com wrote.
For example: https://login.office.microsoft.com.scam.co/microsoft-outlook-login/
Scammers can fake anything before the second-to-last dot in the URL and after the first single-slash line, including tossing in “microsoft” and “outlook” to try to confuse you. However, they cannot fake what comes between them: the actual suffix of the registered URL. Scammers cannot eliminate the suffix of the real source of the link. They can only hide it between a bunch of characters.
So in the example, the REAL destination would be “scam.co,” not Microsoft. The “scam.co” comes after the second-to-last dot and before the first single-slash line.
When I hovered my cursor over the “Keep Active Password” button, a URL did indeed pop up. Using DigitalCheck.com’s rule to read only what comes between the second-to-last-dot and the first single-slash line, I could see the button link did NOT lead to Microsoft.
Instead, it led me to my delete button — and to a whole new way of fishing out a phishing scam.
Copyright 2021 Wise ChoicesTM. All rights reserved.
andy does it work, andy will it work, andy wise, andy wise channel 3, andy wise channel 5, andy wise choices, andy wise memphis, andy wise on your side, andy wise reporter, consumer investigator andy wise, consumer protection, does it work, does it work thursday, outlook phishing email, phishing, phishing scams, wise choices